

Edit: oh that just means they’re above the required threshold already.
Thanks for the clarification. I needed that.


Edit: oh that just means they’re above the required threshold already.
Thanks for the clarification. I needed that.


They shouldn’t play with our food. Food is not a toy.
Yes, that’s the body position where the spider silk is made. But spiderman is wearing trousers (and underpants I suppose).
There was a (ig nobel prize winning?) study which asked the question if someone could pollute a clean or sterile environment by farting into it: The team of scientists concluded that it is safe (regarding… particles) as long as you wear underpants/ trousers. (https://www.ncbi.nlm.nih.gov/pmc/articles/PMC1121900/)
So…


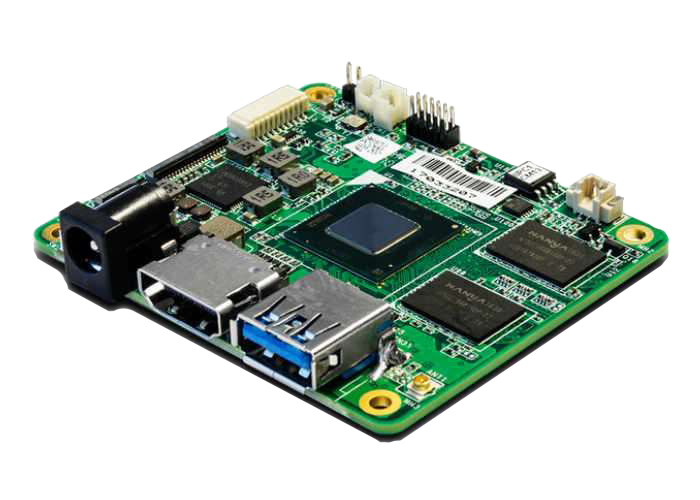
:) the hardware is still more capable than a brick:
Plug in favourite installation media stick, push reset button (if there is one), reinstall.


Can an OS be bricked?:
A brick (or bricked device) is a mobile device, game console, router, computer or other electronic device that is no longer functional due to corrupted firmware, a hardware problem, or other damage.[1] The term analogizes the device to a brick’s modern technological usefulness.[2]
Edit: you may click the tiny down arrow if you think it can’t. ;)

Q: A or B?
A: Yes.
Mars does not have a strong magnetic field like Earth does, so solar winds can strip away bits of the atmosphere.
I wanted to say the same. And furthermore I wanted to add that it’s beside the point of the comic. But I still wanted to say it.


One aspect is how interesting you are as a target. What would a possible attacker gain by getting access to your services or hosts?
The danger to get hacked is there but you are not Microsoft, amazon or PayPal. Expect login attempts and port scans from actors who map out the internets. But I doubt someone would spend much effort to break into your hosts if you do not make it easy (like scripted automatic exploits and known passwords login attempts easy) .
DDOS protection isn’t something a tiny self hosted instance would need (at least in my experience).
Firewall your hosts, maybe use a reverse proxy and only expose the necessary services. Use secure passwords (different for each service), add fail2ban or the like if you’re paranoid. Maybe look into MFA. Use a DMZ (yes, VLANs could be involved here). Keep your software updated so that exploits don’t work. Have backups if something breaks or gets broken.
In my experience the biggest danger to my services is my laziness. It takes steady low level effort to keep the instances updated and running. (Yes there are automated update mechanisms - unattended upgrades i.e. -, but also downwards compatibility breaking changes in the software which will require manual interactions by me.)

This is not always the case, however, as some individuals may have more spots, fewer spots, or none at all, presumably due to genetic variation.
Or malice. ;)
Thank you for the explanation.

Not saying you are wrong.
But this one has eight spots. Did the bug do it to thwart those naming and categorization efforts?


You might be confusing public IP addresses with ports?
I mean publicly addressable address like in: not in a private network where SNAT/ masquerading is in place between the torrent-client’s host and the Internet.
It was mentioned, that no port forwarding is in place.


Not sure why you would sometimes see your status as fully connectable
One side of the connection needs a public address, not both. When both parties don’t have a publicly addressable IP, the status is firewalled. I guess.
He used an inch tape measure and converted the height to cm I guess.
Let the patch be part of the code for one or two minor releases. Then revert the changes of the patch.


Nice!
It’s the little things that make your day.


I assume you want to access a self hosted service on your local server from the Internet.
To make the service accessible from the Internet multiple things are required:
10-15 is good enough. :)